- Decrypt Max Script Motorola Software Update Download Defy The Boss Baby Watch Online Movie Bluray Gm Global Tis Keygen Software Mac Windows 95 Floppy Disk Images Download Passlock.download.5233 Cara Mendownload Aplikasi Samsung Galaxy Ace Talking Dictionary English To Bengali.
- With this script you can reset all materials in your marerial editor to the Materials what you using in your workflow. For now you can reset to Standart marerials, Vray materials, Corona materials, Mental Ray, FStorm, or Arnold materials. This script is tested at 3ds max 2016 and 3ds max 2021. Version 1.0 - reset to Standart marerials.
Disable forced encryption of data partition. Get little better performance and internal sd + data mounting in TWRP Things needed: Unlocked Max pro with TWRP flashed Instructions: 1. Download the decrypt.zip and move/copy to sdcard/otg drive 2.
Standard mse encryption in 3DS Max is not safe. There are decryption programs in the internet. It recognize currently opened script in MaxScript Editor and save it as encrypted mse. Salon Iris V9 Keygen on this page. This is not a macro script but. Macroscript QuickEncrypt category:'Pixamoon' tooltip:'Quick Encrypt' buttonText:'QE'. Or use with Favorite. Nice tool,but,believe it or not.mse format does not safe,it's very easy to decrypt.
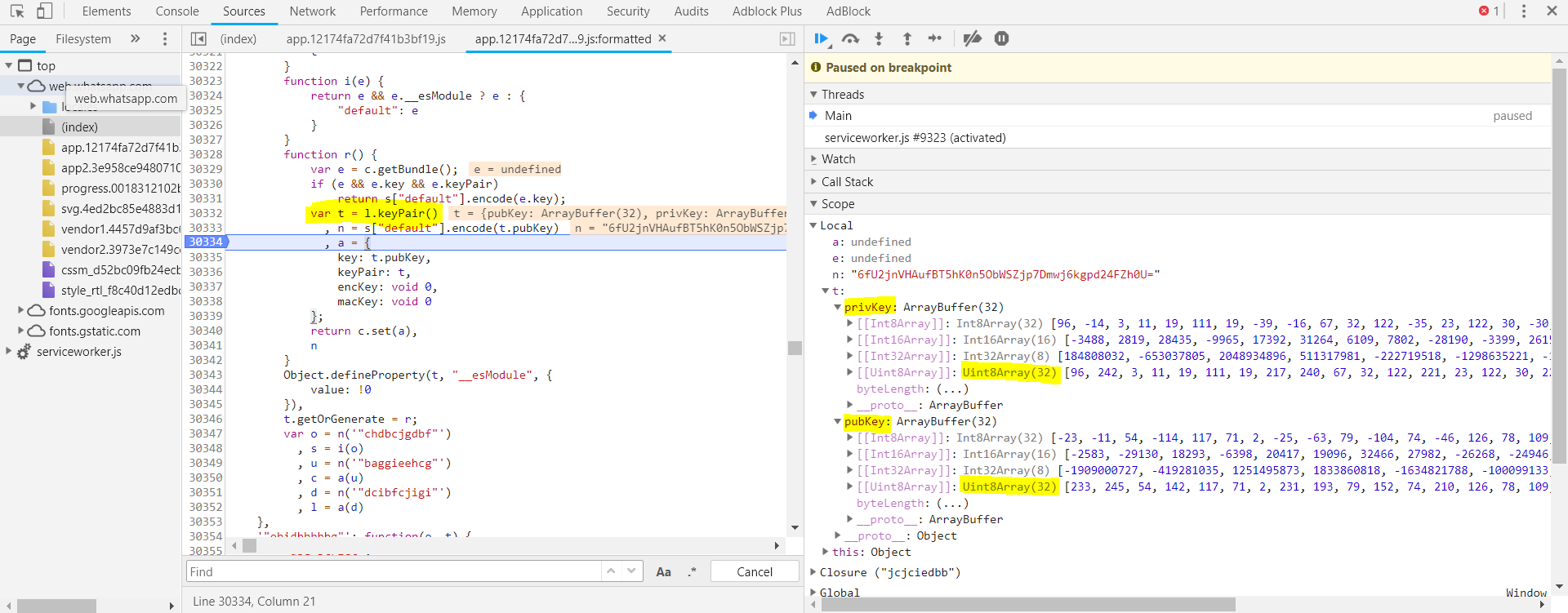

See my comments under the script, definitely wouldn't call that 'without a chance to decrypt' when it's in fact easier to decrypt the result created by this than a.mse file you'd create the usual way.: well, if you make something that's interesting and useful to a number of people, someone will find a way to break the protection and publish the 'open' version. If it's not that interesting, plain old.mse is okay, no one will bother. How To Install Dollhouse Windows. That said, C++ has an edge in this regard as most of the time, the disassembly you will get out of it is not all that useful, unless you are very commited to finding a way around it.
In which case, there will be a keygen or something like that in no time either way. Theatre Of War 2 Africa 1943 Key License. There's also minification and obfuscation which you can use together with saving the file as.mse, though that would only help if you want to make it hard for people to copy-paste sections of your code, not if you want to make it harder to circumvent a protection you have in place.
Comments are closed.
-->This tutorial covers how to make use of client-side storage encryption with Azure Key Vault. It walks you through how to encrypt and decrypt a blob in a console application using these technologies.
Estimated time to complete: 20 minutes
Decrypt Max Script Free
For overview information about Azure Key Vault, see What is Azure Key Vault?.
For overview information about client-side encryption for Azure Storage, see Client-Side Encryption and Azure Key Vault for Microsoft Azure Storage.
Prerequisites
To complete this tutorial, you must have the following:
- An Azure Storage account
- Visual Studio 2013 or later
- Azure PowerShell
Overview of client-side encryption

For an overview of client-side encryption for Azure Storage, see Client-Side Encryption and Azure Key Vault for Microsoft Azure Storage
Here is a brief description of how client side encryption works:
- The Azure Storage client SDK generates a content encryption key (CEK), which is a one-time-use symmetric key.
- Customer data is encrypted using this CEK.
- The CEK is then wrapped (encrypted) using the key encryption key (KEK). The KEK is identified by a key identifier and can be an asymmetric key pair or a symmetric key and can be managed locally or stored in Azure Key Vault. The Storage client itself never has access to the KEK. It just invokes the key wrapping algorithm that is provided by Key Vault. Customers can choose to use custom providers for key wrapping/unwrapping if they want.
- The encrypted data is then uploaded to the Azure Storage service.
Set up your Azure Key Vault
In order to proceed with this tutorial, you need to do the following steps, which are outlined in the tutorial Quickstart: Set and retrieve a secret from Azure Key Vault by using a .NET web app:
- Create a key vault.
- Add a key or secret to the key vault.
- Register an application with Azure Active Directory.
- Authorize the application to use the key or secret.
Make note of the ClientID and ClientSecret that were generated when registering an application with Azure Active Directory.
Create both keys in the key vault. We assume for the rest of the tutorial that you have used the following names: ContosoKeyVault and TestRSAKey1.
Create a console application with packages and AppSettings
In Visual Studio, create a new console application.
Add necessary nuget packages in the Package Manager Console.
Add AppSettings to the App.Config.
Add the following using directives and make sure to add a reference to System.Configuration to the project.
We are currently working to create code snippets reflecting version 12.x of the Azure Storage client libraries. For more information, see Announcing the Azure Storage v12 Client Libraries.
Decrypt Max Script
Add a method to get a token to your console application
The following method is used by Key Vault classes that need to authenticate for access to your key vault.
We are currently working to create code snippets reflecting version 12.x of the Azure Storage client libraries. For more information, see Announcing the Azure Storage v12 Client Libraries.
Access Azure Storage and Key Vault in your program
In the Main() method, add the following code.
We are currently working to create code snippets reflecting version 12.x of the Azure Storage client libraries. For more information, see Announcing the Azure Storage v12 Client Libraries.
Note
Key Vault Object Models
It is important to understand that there are actually two Key Vault object models to be aware of: one is based on the REST API (KeyVault namespace) and the other is an extension for client-side encryption.
The Key Vault Client interacts with the REST API and understands JSON Web Keys and secrets for the two kinds of things that are contained in Key Vault.
The Key Vault Extensions are classes that seem specifically created for client-side encryption in Azure Storage. They contain an interface for keys (IKey) and classes based on the concept of a Key Resolver. There are two implementations of IKey that you need to know: RSAKey and SymmetricKey. Now they happen to coincide with the things that are contained in a Key Vault, but at this point they are independent classes (so the Key and Secret retrieved by the Key Vault Client do not implement IKey).
Encrypt blob and upload
Add the following code to encrypt a blob and upload it to your Azure storage account. The ResolveKeyAsync method that is used returns an IKey.
We are currently working to create code snippets reflecting version 12.x of the Azure Storage client libraries. For more information, see Announcing the Azure Storage v12 Client Libraries.
Note
If you look at the BlobEncryptionPolicy constructor, you will see that it can accept a key and/or a resolver. Be aware that right now you cannot use a resolver for encryption because it does not currently support a default key.
Decrypt blob and download
Decryption is really when using the Resolver classes make sense. The ID of the key used for encryption is associated with the blob in its metadata, so there is no reason for you to retrieve the key and remember the association between key and blob. You just have to make sure that the key remains in Key Vault.
Decrypt Max Script 2020
The private key of an RSA Key remains in Key Vault, so for decryption to occur, the Encrypted Key from the blob metadata that contains the CEK is sent to Key Vault for decryption.
Add the following to decrypt the blob that you just uploaded.
We are currently working to create code snippets reflecting version 12.x of the Azure Storage client libraries. For more information, see Announcing the Azure Storage v12 Client Libraries.
Note
There are a couple of other kinds of resolvers to make key management easier, including: AggregateKeyResolver and CachingKeyResolver.
Use Key Vault secrets
The way to use a secret with client-side encryption is via the SymmetricKey class because a secret is essentially a symmetric key. But, as noted above, a secret in Key Vault does not map exactly to a SymmetricKey. There are a few things to understand:
- The key in a SymmetricKey has to be a fixed length: 128, 192, 256, 384, or 512 bits.
- The key in a SymmetricKey should be Base64 encoded.
- A Key Vault secret that will be used as a SymmetricKey needs to have a Content Type of 'application/octet-stream' in Key Vault.
Here is an example in PowerShell of creating a secret in Key Vault that can be used as a SymmetricKey.Please note that the hard coded value, $key, is for demonstration purpose only. In your own code you'll want to generate this key.
In your console application, you can use the same call as before to retrieve this secret as a SymmetricKey.
We are currently working to create code snippets reflecting version 12.x of the Azure Storage client libraries. For more information, see Announcing the Azure Storage v12 Client Libraries.
Next steps
For more information about using Microsoft Azure Storage with C#, see Microsoft Azure Storage Client Library for .NET.
For more information about the Blob REST API, see Blob Service REST API.
For the latest information on Microsoft Azure Storage, go to the Microsoft Azure Storage Team Blog.